BLOG
Which Sectors are Really Prioritising on Cyber Security
Jul 24 2017
Darren Best

The Consequences of a Cyber-Attack
A cyber-attack is usually a deliberate attempt to exploit the computer systems and/or network infrastructure of an individual, organisation or public entity for the purpose of attaining sensitive information/data. Depending on how sophisticated a cyber-attack may be, the consequences can be very disruptive and lead to substantial financial as well as reputational losses arising from: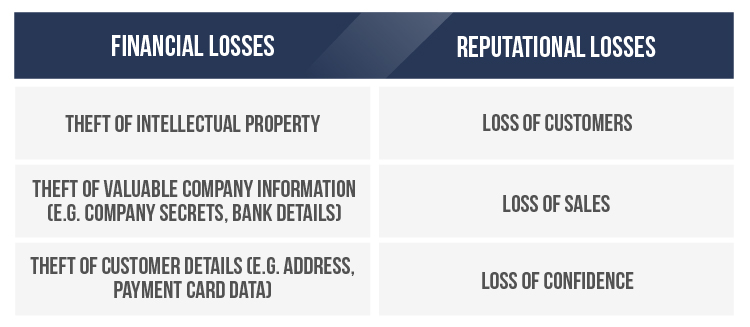 Interestingly, according to security professionals consulted by networking hardware company Cisco, operations of an organisation (36%) are most likely to be affected by any potential cyber-attack/breach. After operations - finances (30%), brand reputation (26%), customer retention (26%) and intellectual property (24%).
Interestingly, according to security professionals consulted by networking hardware company Cisco, operations of an organisation (36%) are most likely to be affected by any potential cyber-attack/breach. After operations - finances (30%), brand reputation (26%), customer retention (26%) and intellectual property (24%).
How Cyber Criminals are Operating
In a recent report published by the National Crime Agency, they state that Cyber Criminals “technical sophistication varies from small scale cyber-enabled fraud to persistent, advanced and professional organisations”. This provides clear context into the levels of threat that cyber criminals may potentially embody. Whilst they are often unpredictable, where there is opportunity, they will seek to inflict damage. Additionally, their ambitions could potentially stretch beyond just technological weaknesses (e.g. outdated software), they worryingly may also target people (e.g. malicious links to employee emails). Photo Credit: Alexander Geiger / Shutterstock
Photo Credit: Alexander Geiger / Shutterstock
Case Studies
Tesco Bank (2016)
In 2016, Tesco Bank admitted that an estimated £2.5 million had been stolen from 9,000 customer accounts. The bank did not elaborate on the attack but only confirmed it was subject to ‘criminal activity’. Regardless, it is still considered one of the biggest cyber-attacks of its kind to affect a UK bank. Adrian Davis, Managing director for EMEA (ISC)2 (the independent body for ‘Information Security Professionals) commented critically on the Tesco Bank breach: “They have not realised just how much their organisations have changed in the digital age and how this is leaving them vulnerable. They have not treated cyber risk as anything more than an IT problem, and now they, and we, are paying the price”.Three Mobile (2016 and 2017)
One of Britain’s large mobile phone companies Three, reported in 2016 that it had experienced a large cyber-security breach. The company admitted that the perpetrators had successfully accessed its vast customer upgrade database after using a Three employees login details. Three stated no financial information had been taken but the accessed database included names, phone numbers, address and dates of birth. As of 2017, Three believe that of its nine million customers, the data of 210,200 people was compromised as a consequence of the breach.Cyber Security by Sector
With the threat of cyber-attacks and breaches more apparent than ever before, business leaders cannot afford to wait until something drastic happens to react. They should continually prioritise cyber security at the heart of their operations and ensure they are not vulnerable to potential attacks/breaches. Bearing this in mind, SavoyStewart.co.uk sought to find out the attitudes of directors/senior management in a range of sectors towards cyber security. This was achieved through analysing the 2017 ‘Cyber Security Breaches Survey’ to reveal: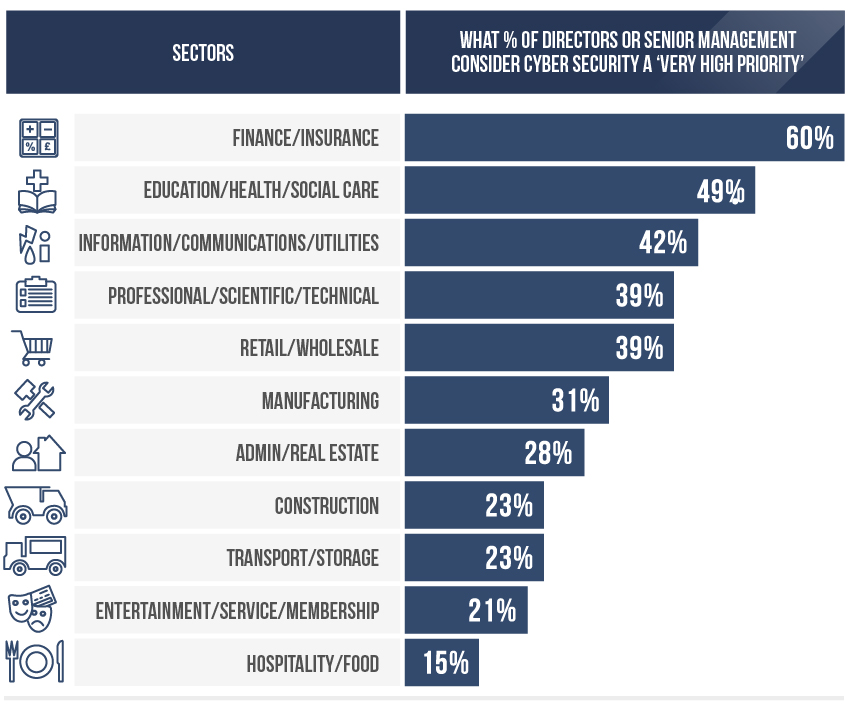 60% of directors/senior management in finance and insurance consider cyber security as a very high priority for their respective organisations – the highest amongst the varying sectors. Thereafter, directors/senior management within education, health or social care most consider cyber security as a very high priority at just under 50%.
With only 15% of directors/senior management in the hospitality and food sectors classifying cyber security as a very high priority, it seems they are the least concerned by prospective threats. Those directors/senior management operating in the entertainment, service or membership sectors are only slightly more apprehensive – with 21% stating cyber security as a very high priority for them and their operations.
60% of directors/senior management in finance and insurance consider cyber security as a very high priority for their respective organisations – the highest amongst the varying sectors. Thereafter, directors/senior management within education, health or social care most consider cyber security as a very high priority at just under 50%.
With only 15% of directors/senior management in the hospitality and food sectors classifying cyber security as a very high priority, it seems they are the least concerned by prospective threats. Those directors/senior management operating in the entertainment, service or membership sectors are only slightly more apprehensive – with 21% stating cyber security as a very high priority for them and their operations.
Savoy Stewart’s Best Practice Tips for Cyber Security
Constant Motions
Aim to always keep software up to date, apply security patches and frequently change passwords.Apply Limitation
Restrict the functionality of every device, operating system and application to the minimum needed for the business to function.Understand Risk
Conduct regular and through assessments of IT systems. Continually identify any vulnerabilities that maybe be exposed and targeted by opportunistic cyber criminals.Intelligence
Sharing contextual information on potentially critical threats with business peers and industry groups provides greater intelligence to detect as well as respond to incidents more efficiently.Customer Best Practice
Utilise best practice encryption and other security technologies to best protect personal details which are collected online. Also, assist customers with clearly enforcing safe password practises (e.g. using strong and varied passwords).Spread Awareness
Have formal cyber security polices which are clearly documented and regularly reviewed. Make sure employees are actively aware of the cyber security policies and provide full context as to what they are permitted to do on the organisation’s IT devices/systems/networks. Photo Credit: Maksim Kabakou / Shutterstock
Photo Credit: Maksim Kabakou / Shutterstock